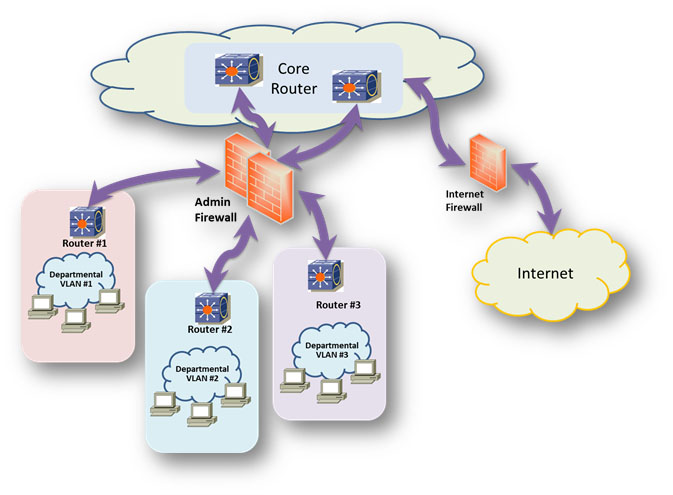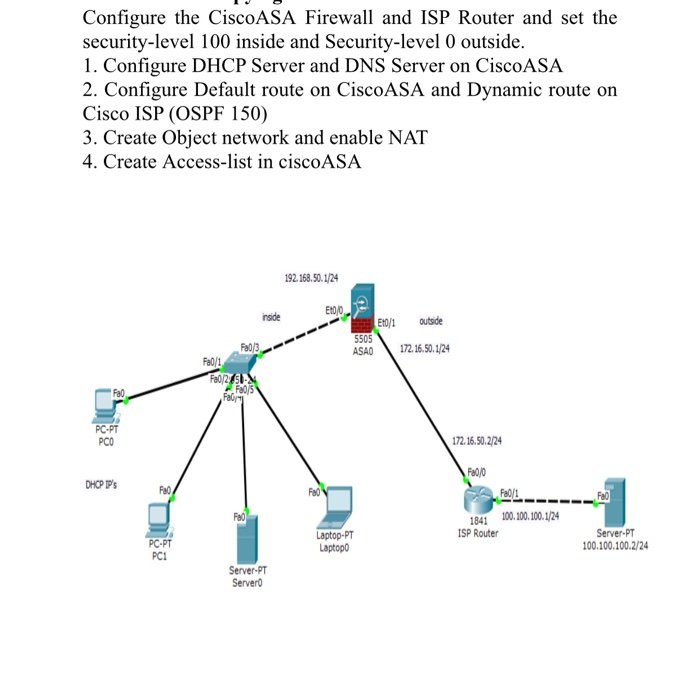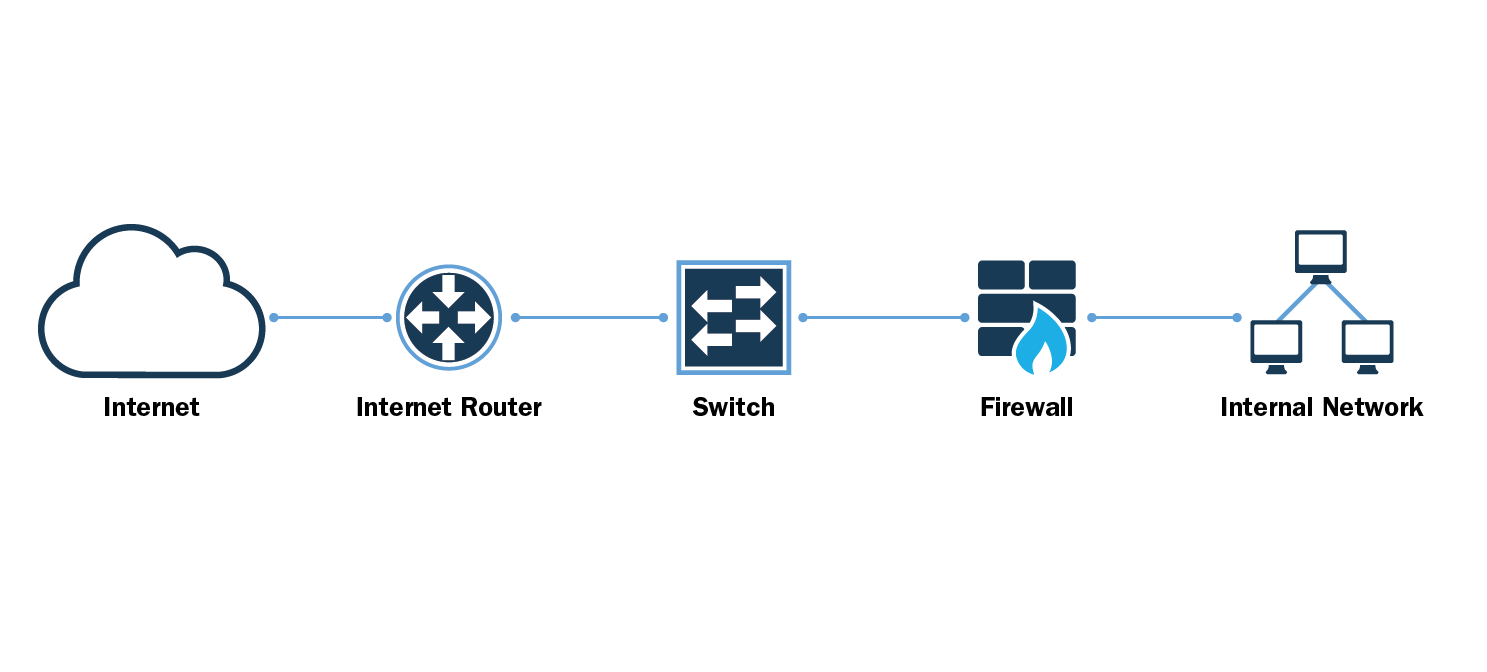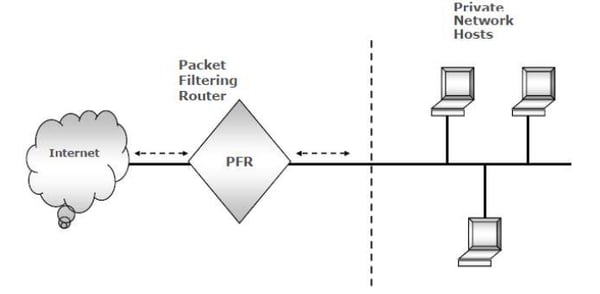
Firewall Design :: Chapter 2. Introduction to Firewalls :: Part I: Security Overview and Firewalls :: Router firewall security :: Networking :: eTutorials.org

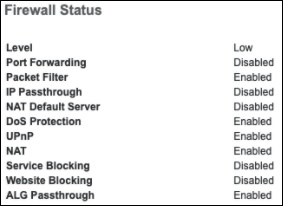
Fortinet FG-80F Entry-Level Switch Router RJ45 Ports | Network Router FortiGate Server Switches Security Firewall Protection Hardware Optimization Business And Office Networks Solution | Red Hardware | Entry Level | Lazada PH
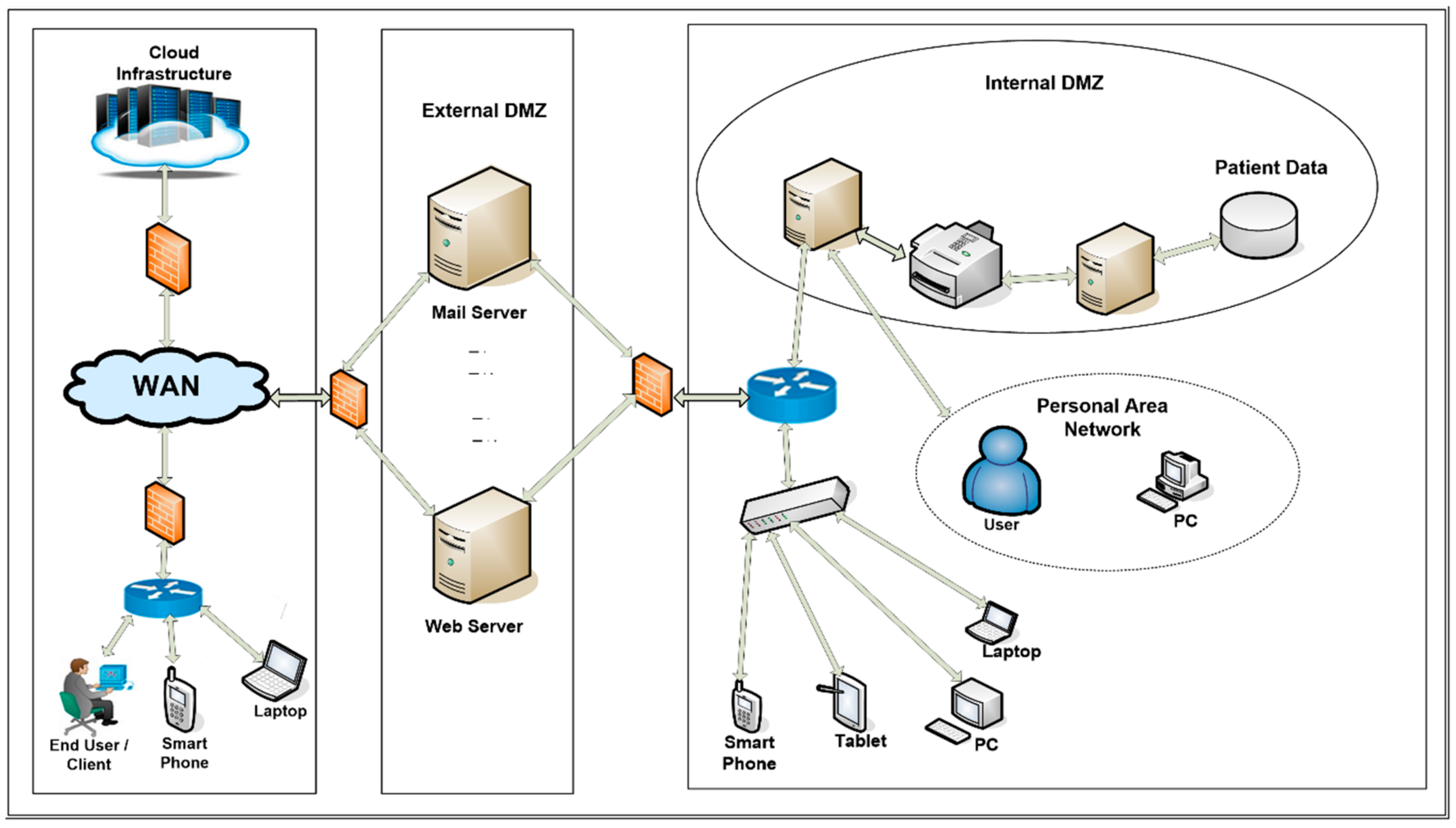
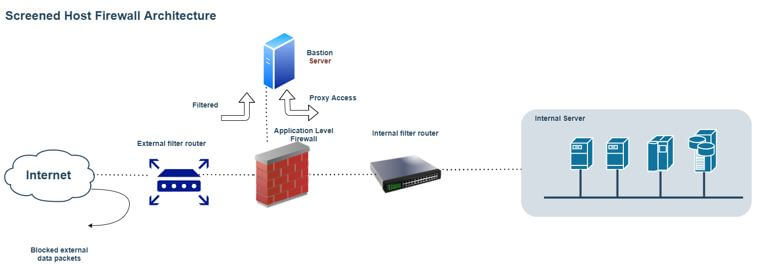
Applied Sciences | Free Full-Text | Firewall Best Practices for Securing Smart Healthcare Environment: A Review